27th December 2003 Ian Wells
This is an introduction to using Public-Private Keys as applied to SSH.
It has been written in response to questions regarding my CVS How-To.
It currently covers the first three steps needed to use Public-Private keys
It also has sections on
The following has been tested using a Mitel SME Server, and Windows XP& RedHat 8.0 clients.
Some sections use PuTTY to connect to the server,
it is a free implementation of SSH for Win32 platforms,
with extensive online documentation.
See Tom Carroll's HowTo for details of how to use PuTTY.
This section describes three ways to generate the public-private key pairs, and specifically a SSH protocol 2 RSA key pair.
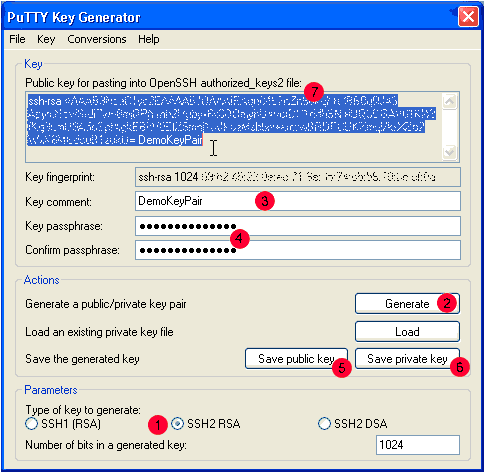 |
PuTTYgen can be used to generate the keys, which is described in detail in Chapter 8.2
|
It is possible to use the SME Server itself to generate the public-private key pairs. This is done by using ssh-keygen.
By default the pair is written to $HOME/.ssh/id_rsa and $HOME/.ssh/id_rsa.pub
bash-2.05a$ ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/home/e-smith/files/users/dummy/.ssh/id_rsa): [Enter to accept default] Created directory '/home/e-smith/files/users/dummy/.ssh'. Enter passphrase (empty for no passphrase): [Your passphrase] Enter same passphrase again: [Your passphrase] Your identification has been saved in /home/e-smith/files/users/dummy/.ssh/id_rsa. Your public key has been saved in /home/e-smith/files/users/dummy/.ssh/id_rsa.pub. The key fingerprint is: aa:bb:cc:dd:ee:ff:aa:bb:cc:dd:ee:ff:aa:bb:cc:dd dummy@gatekeeper
To generate the public-private key pair on a RedHat 8.0 box is identical to the SME Server, as both use OpenSSH.
In this example I have specified the comment field.
$ ssh-keygen -t rsa -C dummy@rh8 Generating public/private rsa key pair. Enter file in which to save the key (/home/dummy/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/dummy/.ssh/id_rsa. Your public key has been saved in /home/dummy/.ssh/id_rsa.pub. The key fingerprint is: aa:bb:cc:dd:ee:ff:aa:bb:cc:dd:ee:ff:aa:bb:cc:dd dummy@rh8
To make use of the Public-Private Key pair the Public keys must be put onto the server that will be accessed. The Public Key file and its contents do not need to be kept secret.
The Public Key needs to be saved in the file $HOME/.ssh/authorized_keys . For the user dummy on an SME Server it would be:
/home/e-smith/files/users/dummy/.ssh/authorized_keys
The directory .ssh should have permissions 700 and the file authorized_keys should have permissions either 644 or 600. If the directory does not exist it can be created as follows, which presumes that you are logged in as yourself, not root.
bash-2.05a$ cd bash-2.05a$ mkdir .ssh bash-2.05a$ chmod 700 .ssh bash-2.05a$ ls -al drwx------ 2 dummy dummy 4096 Feb 18 11:23 .ssh
The authorized_keys file can store multiple public keys, one on each line, so the following examples always append to the end of the file.
Copying the Public Key generated by ssh-keygen, $HOME/.ssh/id_rsa.pub
This example presumes that the key was generated on the server, or has been copied into the $HOME/.ssh directory.
bash-2.05a$ cat id_rsa.pub >> authorized_keys bash-2.05a$ ls -l -rw-r--r-- 1 dummy dummy 225 Feb 18 11:26 authorized_keys
There are two main ways of doing this, they each require that the "Public key for pasting into authorized_keys file"
is copied to the clipboard (see Step 7 on the figure above).
For more details read the PuTTY manual.
One method is to paste the key into a file (putty.pub in the example below).
Then copy this file into the $HOME/.ssh directory on the server. This file can then be appended to the authorized_keys file.
bash-2.05a$ cat putty.pub >> authorized_keys
The other method is simpler but more complicated to explain.
The Private Key needs to be accessible from the clients that you use. The Private Key file should be kept secure, and should be protected by a pass phrase.
Private Key files cannot be directly shared between PuTTY and OpenSSH, however PuTTYgen can convert the files.
In these examples the server is the SME Server, and the clients will be Windows and RedHat 8.0
To start using PuTTY with SME Server see Tom Carroll's HowTo
To use the Private Key go to the PuTTY Configuration and select the Connection - SSH - Auth.
Then in the Private key file for authentication: enter the path to the private key file, or find it using Browse.
When starting the PuTTY terminal the following is shown. You will need to enter the passphrase, if one was set.
Using username "dummy". Authenticating with public key "dummy@homepc" Using the private key generated on my windows machine Passphrase for key "dummy@homepc": Welcome to the Mitel Networks SME Server. Using username "dummy". Authenticating with public key "dummy@gatekeeper" Using the private key generated on my SME Server Passphrase for key "dummy@gatekeeper": Welcome to the Mitel Networks SME Server.
This brief example shows the start of a SSH session where the username is specified using the -l option.
[dummy@homepc dummy]$ ssh -l dummy gatekeeper Enter passphrase for key '/home/dummy/.ssh/id_rsa': Last login: Tue Feb 18 11:38:43 2003 from somewhere Welcome to the Mitel Networks SME Server. bash-2.05a$
Files used by OpenSSH, full details can be found from the
ssh-keygen (1) and
sshd (8)
manual pages.
$HOME/.ssh/id_rsa
This is the private key, it contains the protocol version 2 RSA
authentication identity of the user. This file should not be
readable by anyone but the user.
$HOME/.ssh/id_rsa.pub
Contains the protocol version 2 RSA public key for authentication.
The contents of this file should be added to the authorized_keys file on all machines where the user wishes
to log in using public key authentication.
There is no need to keep the contents of this file secret.
$HOME/.ssh/authorized_keys
Lists the public keys that can be used to log into the user's
account. This file must be readable by root. It is recommended
that it not be accessible by others.
Each line of the file contains one key (empty lines and lines starting
with a `#' are ignored as comments). Each protocol version 2 public key
consists of: options, key-type, base64 encoded key, comment. The comment
field is not used for anything (but may be convenient for the user
to identify the key).
OpenSSH
You can change the passphrase at any time by using the -p option of ssh-keygen.
bash-2.05a$ ssh-keygen -p Enter file in which the key is (/home/e-smith/files/users/dummy/.ssh/id_rsa): [Enter to accept default key file] Enter old passphrase: [Old passphrase] Key has comment '/home/e-smith/files/users/dummy/.ssh/id_rsa' Enter new passphrase (empty for no passphrase): [New passphrase] Enter same passphrase again: [New passphrase] Your identification has been saved with the new passphrase.
PuTTY
To change the passphrase of a PuTTY key use PuTTYgen.
Copyright © 2003
Ian Wells : The original can be found from http://www.wellsi.com/sme
: Please send additions & corrections to me.
Permission
is granted to copy, distribute and/or modify this document under the
terms of the GNU Free Documentation License, Version 1.2 or any later
version published by the Free Software Foundation; with no Invariant
Sections, no Front-Cover Text and no Back-Cover Text. A copy of the
GNU Free Documentation License is available from the Free Software
Foundation at http://www.fsf.org/copyleft/fdl.html.